Manufacturing facilities are under immense pressure to keep the brittle supply chain moving. While they may play a big role in the supply chain, they also depend on raw materials to manufacture products. Unfortunately, many things have disrupted the process including the lack of needed materials and security attacks.
Many manufacturing facilities don’t realize they are as much at risk for security breaches as a company with sensitive data. Because of this, they’re vulnerable to security attacks that could cause physical damage and operational downtime.
7 Ways to Secure Manufacturing Facilities
These facilities need physical security to protect workers, products, and information. Defending a manufacturing facility requires multilayered security. Here are the steps every manufacturing facility must take to protect itself against security risks and the supply chain crisis.
1. Bring in a Security Consultant
Would you have marketing or human resources manage your manufacturing facility’s cybersecurity? Of course not. By the same token, the IT department should not be responsible for physical security. Yes, they’re responsible for cybersecurity, but the team does not have the knowledge you need to design an effective physical security program for a manufacturing facility.
To do manufacturing facility security the right way, bring in a security contractor who has experience working with manufacturing facilities. Every industry has different security requirements and best practices. Even two manufacturing facilities would not have identical security setups. That’s why it’s critical to find someone with experience in manufacturing.
The security consultant with the appropriate experience knows how to customize and optimize security based on your manufacturing facility’s needs and requirements. As you search for a vendor, look for someone who has credentials such as Certified Security Consultant (CSC), Certified Protection Professional, or Physical Security Professional.
2. Conduct a Security Risk Assessment
One thing you’ll want the security consultant to do is to conduct a security risk assessment. The person will review what security technologies you have in your facility and identify potential vulnerabilities. In doing the assessment, the security expert will study crime reports to determine what kinds of crimes occurred in your manufacturing facility’s neighborhood.
The security professional may use a tool like the FBI’s National Incident-Based Reporting System (NIBRS). It has interactive maps based on data from local law enforcement agencies. You can search for your geographic location to pull up the crime data for the neighborhood where your manufacturing facility is located. The system displays the crime rate and the types of crime that have been reported to the local law enforcement agency.
For example, select California and search for Los Angeles agencies. The database has data from the LA County Sheriff’s office, the LA police department, the highway patrol for LA county, and more.
The security consultant may analyze the weather patterns and history in the area for other risks. Understanding the risk for nature-made disasters will help you be better prepared.
Your organization’s risk assessment is not a one-and-done project. Imagine if you created a security plan in the 1990s in the early days of the internet. Physical security and technology continue evolving. Doing a security assessment every year involves reviewing the security program’s performance and find areas for improvement.
3. Create a Security Plan
After completing the risk assessment, you’ll want to craft a security plan. The purpose is to document the layout of the facility’s property to find potential perimeter security vulnerabilities. The security plan also provides a visual way to highlight areas that need better security. It will describe the security requirements for the entire perimeter including the facility and its surroundings. You’ll want to make sure it outlines the process of creating, evolving, and conducting security training for employees on a regular basis.
Here’s why layered security is important as you’ll see in the next item. You can have all the right security technology in place. However, all it takes is one employee’s mistake to bring down security. It can be as simple as allowing someone to piggyback into the facility. People and processes are a vital part of manufacturing facility security’s success. Training employees is essential to its success.
It’s also important to identify the role of the employee who will be responsible for overseeing the security of the facility and its property. It does not require the person to be a security expert. Rather, the person is the point of contact for all security-related issues and conversations.
For example, if the facility has remote video surveillance, then that employee will be the person the trained monitoring operators will contact when a potential problem arises. Sometimes employees are not at the facility due to vacation or an illness. Therefore, the process needs to designate backups for when the person isn’t available.
The main security contact will also be responsible for ensuring new employees undergo security training when onboarding. They will verify current employees receive security training at least once a year. The most important thing about this role is to assign ownership of security-related roles and tasks to one person. That person can delegate as needed.
4. Create a Multilayered Security Program
Security isn’t something you install and say you’re done. If that were the case, manufacturing facilities would be using outdated security technologies that would not deter crime or identify problems. Security is an ongoing program, not a project.
A facility that treats security as a program makes it part of the organization’s culture and processes. Security will advance as new technologies come out and the geographical area’s dynamics change.
The more effective security programs contain multiple layers. The more security layers you have, the less likely your business is at risk for theft, trespassing, and vandalism. Don’t forget about adding security layers to the area outside of the facility.
Your employees have to park their vehicles somewhere. Too often, parking lot and garage security is an afterthought. This is where a lot of crimes can happen. The growing number of smash-and-grabs and catalytic converter thefts occur in parking garages.
Facilities must think about parking security because FBI data shows there were 538,203 violent-crime incidents in 2020. Out of those incidents, 45,107 took place in parking garages and on parking lots. You can reduce your risk for parking lot crimes by proactively designing with parking lot security in mind.
Other areas that need multilayered security are the entrances and the exits. The more entrances you have, the harder it will be to protect the building. Make every effort to limit the number of entry points and ensure they’re properly lit and monitored on security cameras.
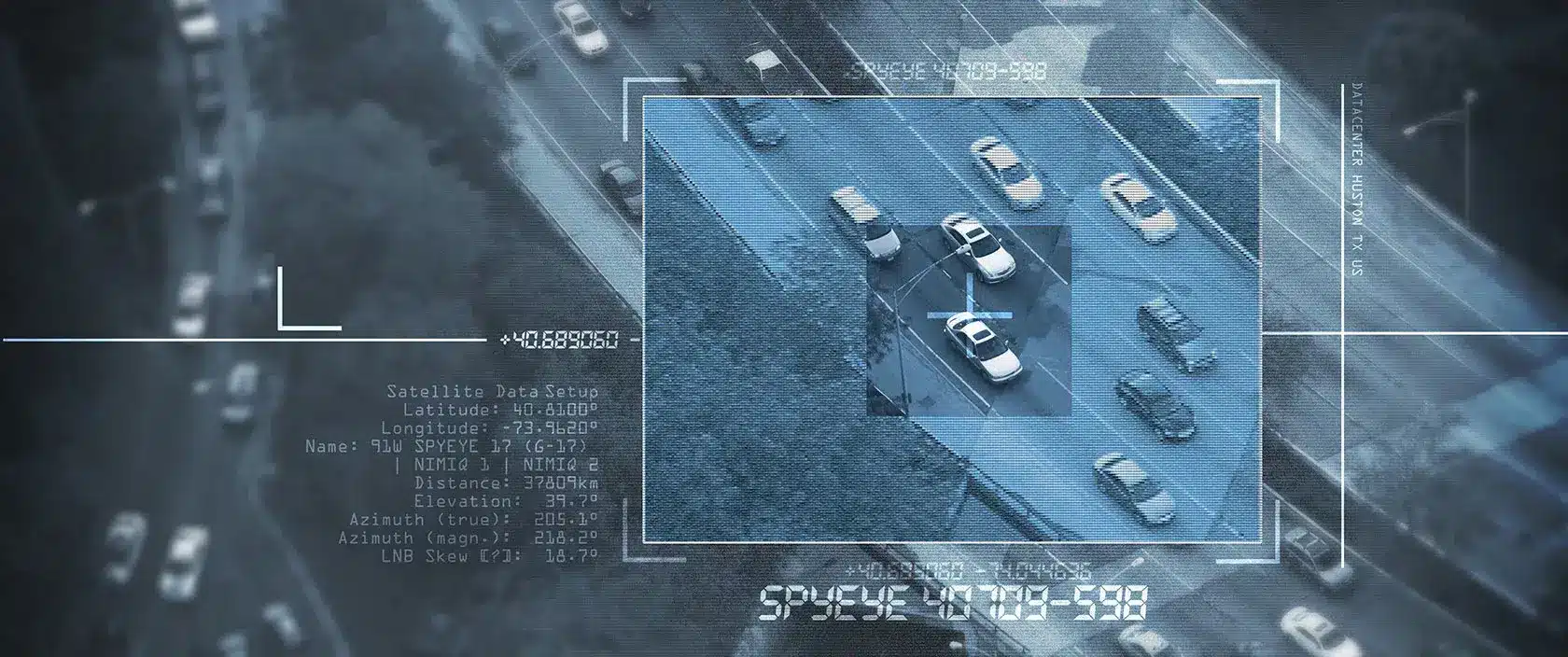
5. Use remote video surveillance
Remote video surveillance is one of the few security options that can do multiple things and add layers to your security. It can help deter crime, lower liability, and boost facility productivity. Security cameras can be posted around the property including the parking areas, entrances, and exits.
The sight of security cameras can act as a deterrent and so does the integrated audio speaker warning. In other words, remote video surveillance does many things. It doesn’t simply put eyes on the perimeter.
It can capture everything in recordings, so you have evidence. It incorporates video analytics to reduce the trained monitoring operator’s load. Working with video analytics, the operator can also find and report safety hazards before someone gets hurt. The system eliminates false alarms and the costs associated with them.
Management can work with the trained monitoring operators to identify opportunities for improving productivity and efficiency. They may use footage in training to show employees the right way to do complete tasks.
6. Add an access control system
An effortless and contactless way to manage access and entry is with an access control system. It allows authorized people to enter the building while restricting access to areas or rooms in the facility, such as a parking garage.
Implementing an access control system offers these benefits:
- Incorporates photo identification.
- Minimizes tailgating and piggybacking.
- Controls external access.
- Authenticates identities with integrated access control.
- Eliminates the need for keys.
- Reduces manual security procedures.
Unlike other automated entry systems, an access control system can track who accesses any area of the facility.
7. Cybersecurity for Physical Security
Companies that invest in remote video surveillance, an access control system, and other security technologies must take steps to protect these systems. That’s why it’s important that when you’re searching for a security vendor, ask about their security processes and procedures.
Inquire about the security of their security cameras and their integration with services on IP networks. They should be keeping the software on the system updated to minimize security vulnerabilities. Cybersecurity doesn’t work in a silo. Hackers will try to break into the facility to access data. This is why the convergence of physical and cybersecurity is important. Security cameras will help reduce the risk of cyber-attacks.
The Most Effective Manufacturing Facility Security
One of the most cost-effective solutions that will yield a faster ROI on your manufacturing facility security is remote video surveillance. It offers round-the-clock coverage across the entire property, both the facility and the area around it including parking and the loading zones.
When you opt for remote video surveillance, you gain a proactive security solution that can deter crime before it happens. Traditional security systems are reactive solutions. They don’t respond until after something happens.
The important factor of this technology is remote monitoring. If no one monitors the cameras, then it turns the technology into passive security that could become a liability problem. When you don’t have video analytics working with humans to watch the cameras, then it could become a liability problem because it gives people a false sense of security. That’s why remote video surveillance lowers liability.
Stealth’s security experts can analyze your facility and perimeter to develop a right-sized security solution. In choosing to work with us, you’ll have access to security professionals who have experience in securing industrial facilities. To learn about access control systems, video surveillance, and security solutions that meet your needs, contact us.